Every profile featured on EscortHer goes through a careful verification process to ensure authenticity. We review photos, personal details, and contact information so that users can interact confidently with listings that are accurate and up to date. This quality-first approach helps maintain a reliable environment for exploring companions from cities such as Mumbai, Delhi, Bangalore, Hyderabad, and more.
The platform is designed with user convenience in mind. Smooth navigation, intuitive filters, and well-structured categories make it easy to find companions suited for social engagements, travel company, professional events, or general companionship. EscortHer prioritizes discretion, presenting listings in a respectful and professional manner without unnecessary clutter or explicit content.#delhiescorts@https://escorther.com/esco...
🔗 Visit : https://kanhasoft.com/web-...

Top Web Scraping Services | AI-driven Data Scraping Company
Our AI-powered web scraping company builds custom, compliant scripts that follow site terms for fast, legal, and efficient web data extraction services.
https://kanhasoft.com/web-scraping-services.htmlIt’s a data-driven, ad-powered, creator-friendly, and AR-first machine built for the next generation of the #internet .
I’ve been analysing different #apps for PratsDigital, and Snapchat genuinely has one of the most unique #business models in the social media world. It’s not like Instagram, not like TikTok and definitely not like Facebook.
In this #article , I’ll break down Snapchat’s business model in a very simple and easy-to-understand way the way I explain it to my #seo clients when discussing platform strategies.
https://pratsdigital.in/in...
The reason?
A sharp, evolving, and highly data-driven #marketing #strategy .
In this #article , I’ll break down Netflix’s current marketing strategy (2025) with a approach covering everything from #content strategy to #technology , partnerships, social media, and #growth tactics.
https://pratsdigital.in/ne...
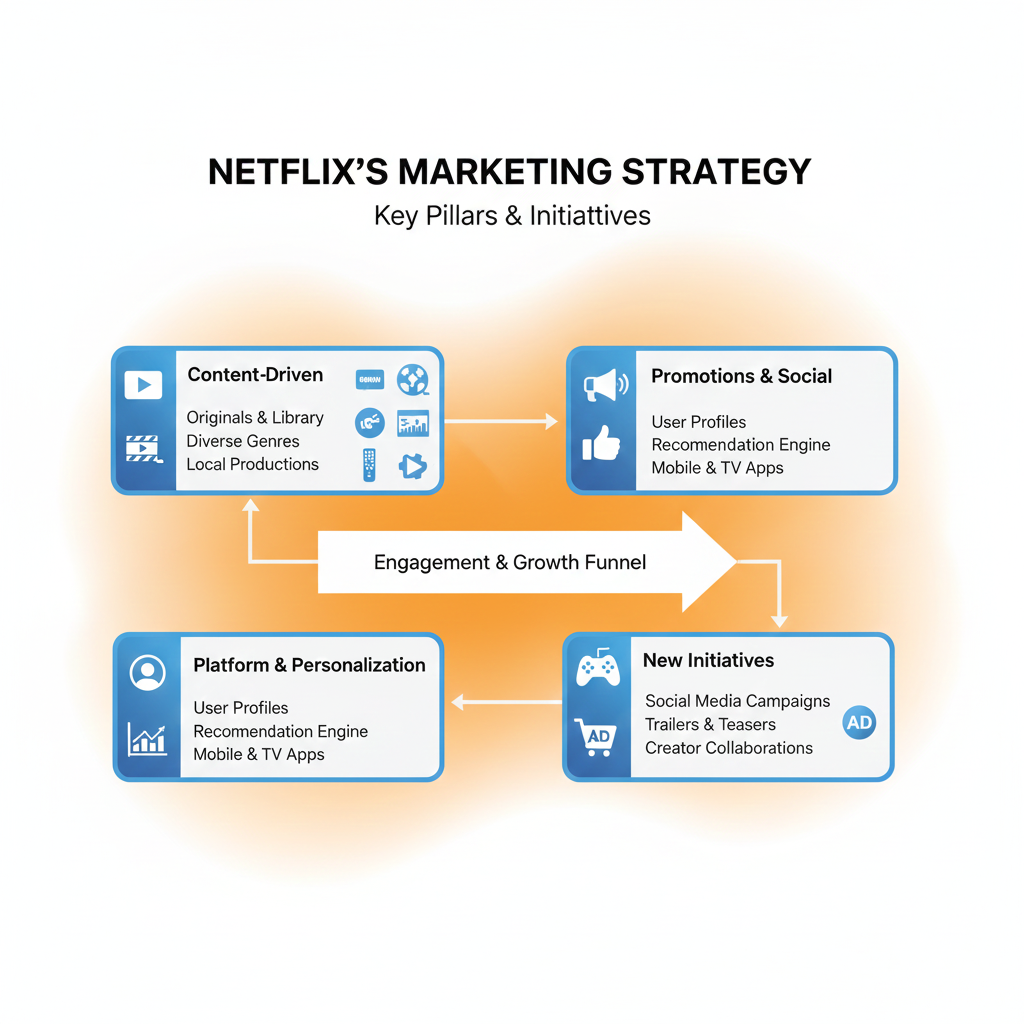
Netflix’s Current Marketing Strategy (2025): A Complete Breakdown - PratsDigital
Netflix’s current marketing strategy explained: data-driven personalization, global content, ad-tier expansion, partnerships, and social media innovations.
https://pratsdigital.in/netflix-current-marketing-strategy/Use our OLX Clone Script to build your own buy-sell marketplace. Take advantage of secure payments, simple listings, advanced search, and complete customization. It facilitates the quick and simple launch of a profitable online classifieds platform with a variety of revenue options.
Black Friday just got more profitable! Grab up to 50% OFF on our OLX clone script and start your own revenue-generating marketplace today.
Free Demo: https://www.trioangle.com/...
Contact: salestrioangle.com
#OLX Clone Script #Buy and Sell Marketplace #Classified Script #online Classifieds Marketplace Script #Buy Sell Platform Clone App Development #online Marketplace
Koinkart is the perfect partner for businesses wanting a Bet365 Clone App packed with featured gaming events and esports matchups. The system is designed to promote trending games, helping you attract more users effortlessly.
Key Features:
Trending esports events on spotlight banners
Real-time game analytics & player performance data
High-speed gaming engine for smooth experience
Fully customizable gaming interface
Get Live Demo or Quote Now!
Website: https://www.koinkart.org/b...
WhatsApp: +91 93842 63771
Mail: businesskoinkart.org
Build a white-label, on-demand food delivery platform like DoorDash with full source-code ownership. OyeLabs’ DoorDash Clone supports Web, iOS & Android, offers real-time order tracking, in-app payments, delivery logistics, restaurant management, and a powerful admin dashboard. Go live quickly, scale your business, and control your brand.
🔗 https://oyelabs.com/doorda...
#FoodDelivery #OnDemandDelivery #startup #WhiteLabelApp #RestaurantTech
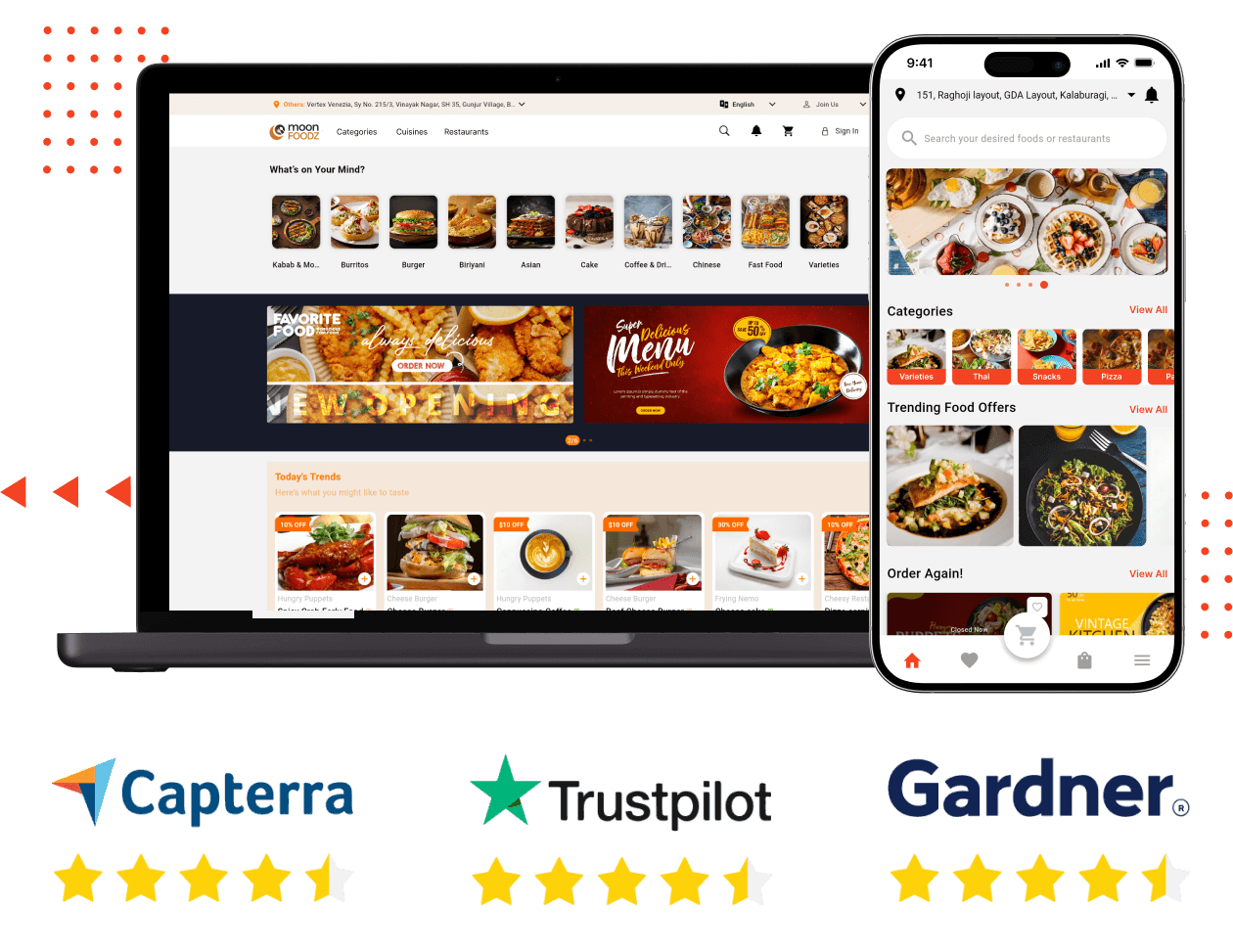
Doordash Clone - Readymade Food Ordering and Delivery App
Doordash clone script is loaded with new-gen features and comes with 100% customizability and free support for 30 days. Launch food delivery business in 3 days.
https://oyelabs.com/doordash-clone/Want to create a full-featured live-shopping app where sellers can stream and sell products in real time? OyeLabs’ Whatnot Clone is a white-label, fully customizable solution (Web + iOS + Android) that comes with full source-code ownership. It offers low-latency streaming, live bidding or auctions, inventory management, seller wallets, real-time notifications, and a robust admin dashboard — perfect for building a modern live-commerce marketplace.
🔗 https://oyelabs.com/whatno...
#LiveCommerce #ecommerce #MarketplaceStartup #WhiteLabelApp #LiveShopping
Looking to build a reliable, full-fledged home-services app (cleaning, plumbing, repairs, beauty services, and more)? OyeLabs’ UrbanClap Clone gives you a white-label, fully customizable platform with complete source-code ownership. With support for Web, iOS, and Android — you get real-time booking, service provider management, secure payments.
🔗 https://oyelabs.com/urbanc...
#OnDemandServices #HomeServices #MarketplaceStartup #WhiteLabelApp #ServiceApp
Read more: https://www.spotnrides.com... https://wa.me/919600695595
#SpotnRides #Uberfortowtruck #OnDemandTowTruckApp #Towtruckbookingapp #TowingserviceapplikeUber #Roadsideassistanceapp #Towtruckdispatchplatform #Towtruckhailingapp #Uberstyletowtruckservice #Towingserviceaggregator #Towtruckoncallapp #Towingservicemarketplace #Roadsiderecoveryapp #Vehicletowingapp #towtruckappforemergencies #Towtruckconnectionservice #CarRescueApp
Book your free call: https://www.beleaftechnolo...
Whatsapp: +917904323274
Mail to: businessbeleaftechnologies.com
End-to-end ICO development that covers tokenomics, smart contracts, landing pages, and marketing support for a powerful fundraising launch.
Discover how we can elevate your ICO today!
https://www.blockchainappf...
#ICOCreation #TokenSale #CryptoProjects
End-to-end ICO development that covers tokenomics, smart contracts, landing pages, and marketing support for a powerful fundraising launch.
Discover how we can elevate your ICO today!
https://www.blockchainappf...
#ICOCreation #TokenSale #CryptoProjects
Visit - https://www.spotnrides.com
WhatsApp: https://wa.me/919600695595
#uberclone #uberclonescript #lyftclone #LyftCloneScript #CarpoolingApp #VoiceBookingApp #OnDemandTaxiApp #ubercloneapp #lyftcloneapp #RideSharingApp #SpotnRides #AppDevelopment #TransportApp #OnDemandApp #cabifyclone #cabifycloneapp #CabifyCloneScript #taxidispatchsoftware #TaxiDispatchSystem #SpotnRides #OnDemandTaxiApp
Want to create a full-featured live-shopping app where sellers can stream and sell products in real time? OyeLabs’ Whatnot Clone is a white-label, fully customizable solution (Web + iOS + Android) that comes with full source-code ownership.
🔗 https://oyelabs.com/whatno...
#LiveCommerce #ecommerce #MarketplaceStartup #WhiteLabelApp #LiveShopping
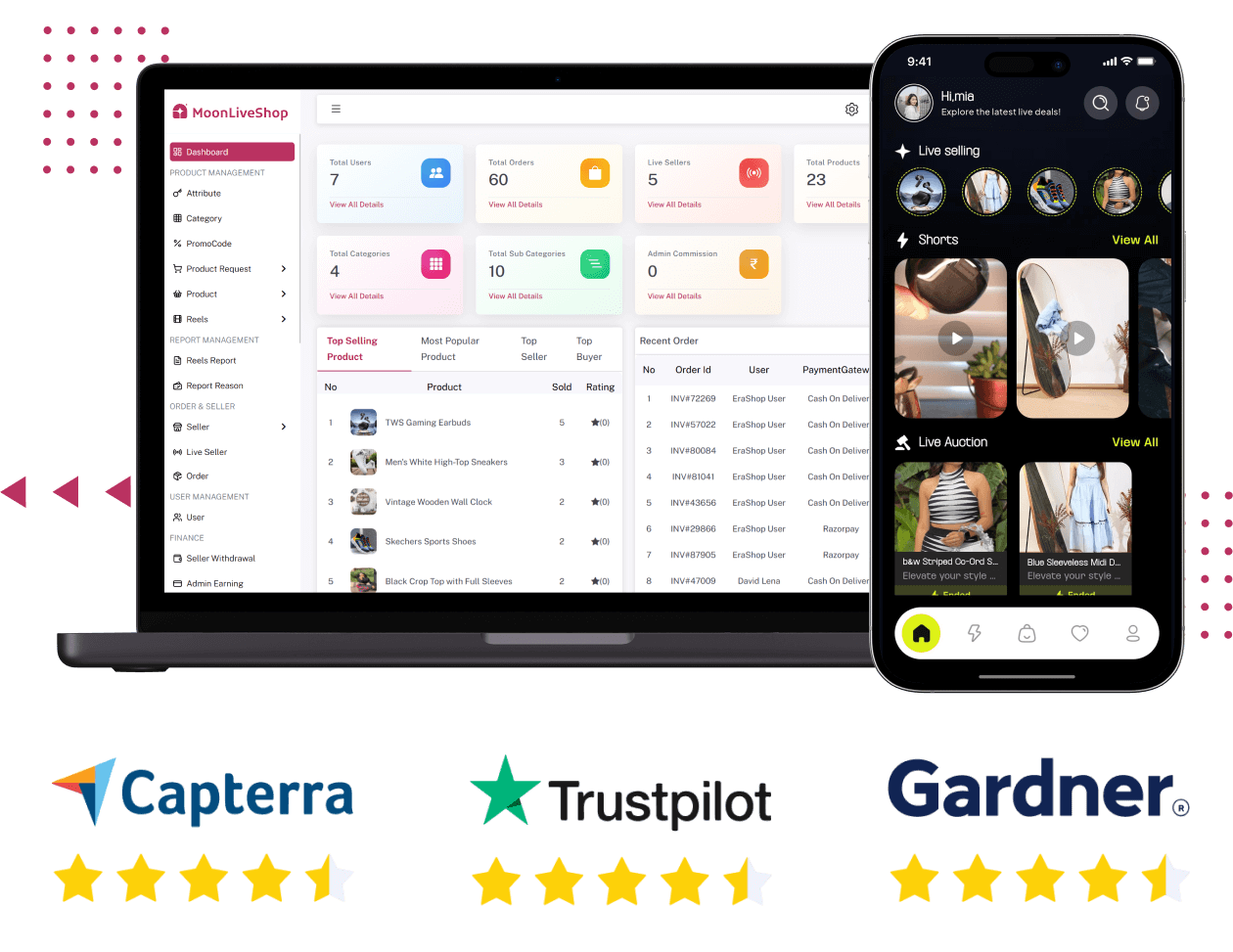
Whatnot Clone - Start Live Shopping Platform in 10 Days
Whatnot clone to build your own live commerce platform with real-time streaming, 100% customizable modules, quick launch setup, and 2 months free support.
https://oyelabs.com/whatnot-clone/Looking to build a reliable, full-fledged home-services app (cleaning, plumbing, repairs, beauty services, and more)? OyeLabs’ UrbanClap Clone gives you a white-label, fully customizable platform with complete source-code ownership. With support for Web, iOS, and Android — you get real-time booking, service provider management, secure payments, and an intuitive admin dashboard. Launch fast — in just 7 days — and start connecting customers with service providers.
🔗 https://oyelabs.com/urbanc...
#OnDemandServices #HomeServices #MarketplaceStartup #WhiteLabelApp #ServiceApp
Visit us: https://www.spotnrides.com...
Whatsapp: https://wa.me/919600695595
#LaundryAppClone #LaundryBusiness #OnDemandLaundryApp #uberforlaundry #UberForLaundryApp #UberforLaundryServices #laundrybookingsoftware #laundrymanagementsoftware #LaundryAppDevelopment #uberforlaundryappsolution #laundrybookingmanagementsystem #LaundryApp
Get a high-performance Uber Clone App built with advanced features like live tracking, driver ratings, secure payments, and smart routing. Delivered with white-label branding and full source code for complete ownership. Visit our website for more information: https://whitelabelfox.com/...
#ubercloneapp #UberLikeApp #uberclonescript #uberclone #uberapp #taxibookingapp #ondemandubercloneapp #ondemandtaxibookingapp #ubercloneappdevelopmentcompany #ubercloneappscript #taxibookingsoftware #taxibookingbusiness
Start a platform that connects users with service providers for cleaning, plumbing, babysitting, handyman work, and more. OyeLabs’ TaskRabbit Clone is a white-label, fully customizable solution (Web + iOS + Android) with complete source-code ownership. It supports real-time bookings, secure payments, provider listings, calendar availability, in-app chat, and an admin dashboard for managing users, services & payouts.
https://oyelabs.com/taskra...
#OnDemandServices #GigEconomy #ServiceMarketplace #startup
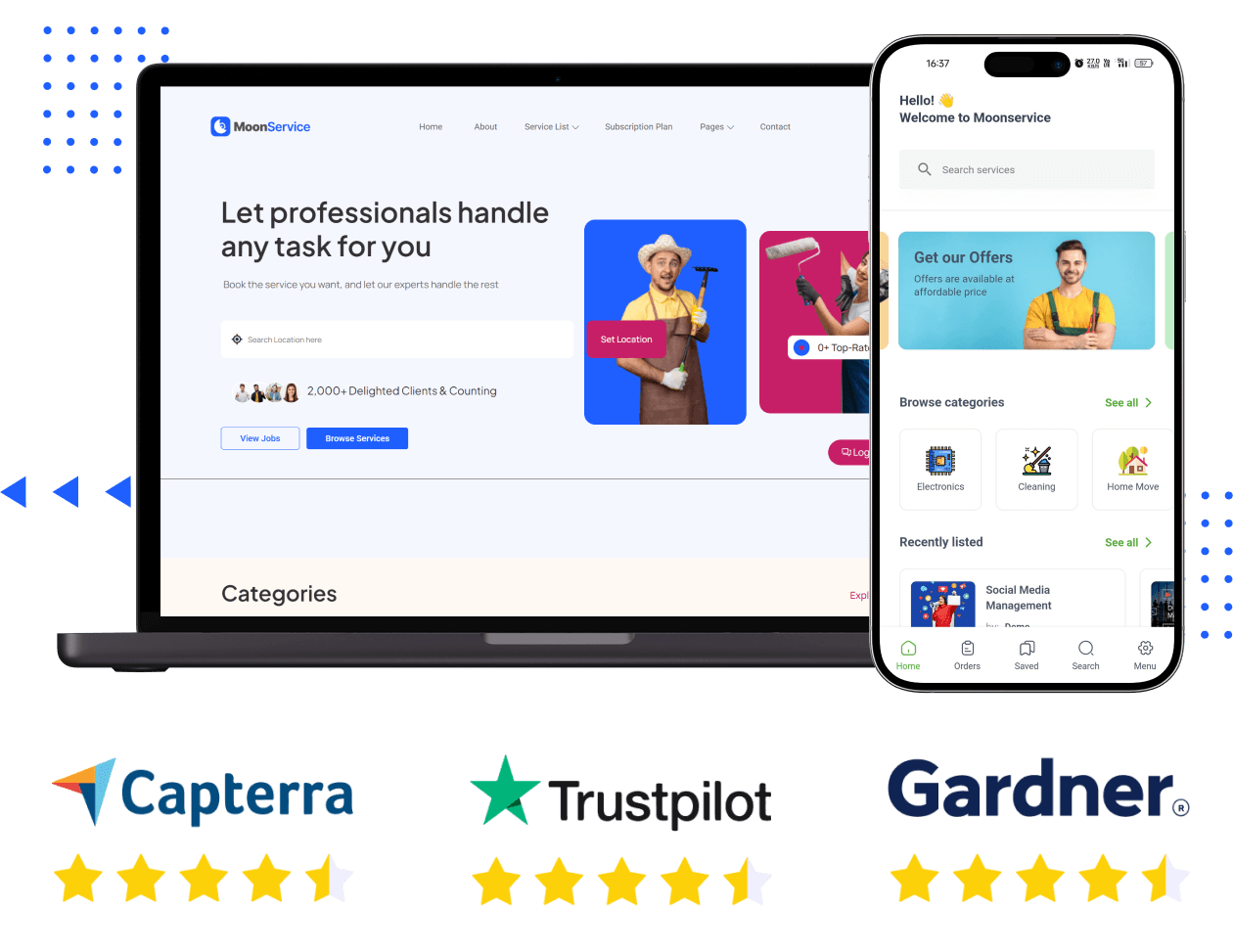
TaskRabbit Clone - Launch Your On-Demand Services Platform
TaskRabbit clone script is a 100% customizable, ready-to-go on-demand service marketplace platform to launch your local app connecting users and professionals.
https://oyelabs.com/taskrabbit-clone/Build a white-label, on-demand food delivery platform like DoorDash with full source-code ownership. OyeLabs’ DoorDash Clone supports Web, iOS & Android, offers real-time order tracking, in-app payments, delivery logistics, restaurant management, and a powerful admin dashboard. Go live quickly, scale your business, and control your brand.
🔗 https://oyelabs.com/doorda...
#FoodDelivery #OnDemandDelivery #startup #WhiteLabelApp #RestaurantTech
Want to build a real-time, live-commerce app where creators can stream and sell products like on Whatnot? OyeLabs’ Whatnot Clone offers a scalable, white-label solution with full source code ownership. You get Web, iOS & Android support, low-latency streaming, real-time bidding, inventory sync, seller wallets, and admin analytics — with deployment in just 10 days.
https://oyelabs.com/whatno...
#LiveCommerce #ecommerce #startup #WhiteLabelApp #StreamingStore
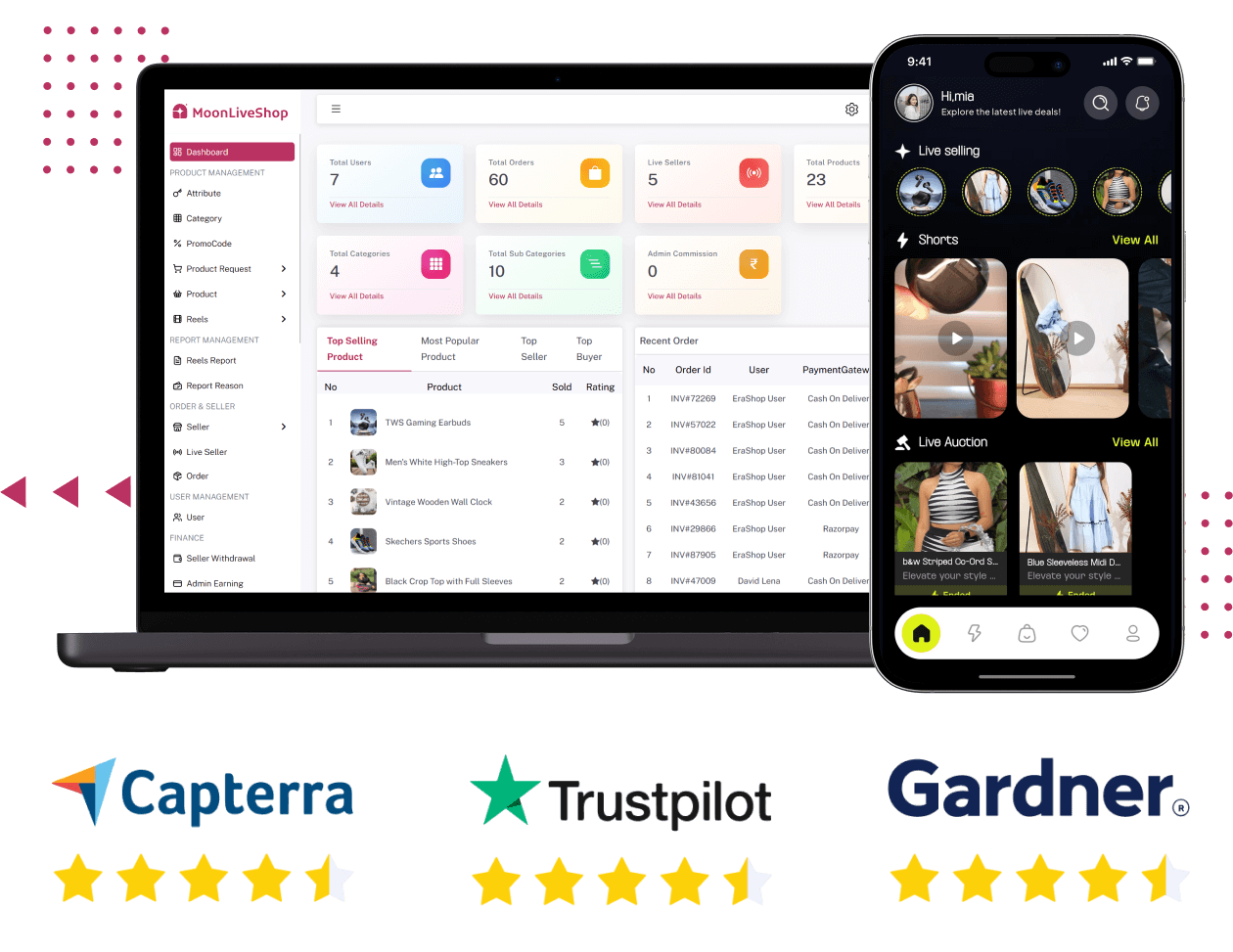
Whatnot Clone - Start Live Shopping Platform in 10 Days
Whatnot clone to build your own live commerce platform with real-time streaming, 100% customizable modules, quick launch setup, and 2 months free support.
https://oyelabs.com/whatnot-clone/Start a platform that connects users with service providers for cleaning, plumbing, babysitting, handyman work, and more. OyeLabs’ TaskRabbit Clone is a white-label, fully customizable solution (Web + iOS + Android) with complete source-code ownership. It supports real-time bookings, secure payments, provider listings, calendar availability, in-app chat, and an admin dashboard for managing users, services & payouts.
https://oyelabs.com/taskra...
#OnDemandServices #GigEconomy #ServiceMarketplace #startup #WhiteLabelApp
Build a white-label, on-demand food delivery platform like DoorDash with full source-code ownership. OyeLabs’ DoorDash Clone supports Web, iOS & Android, offers real-time order tracking, in-app payments, delivery logistics, restaurant management, and a powerful admin dashboard. Go live quickly, scale your business, and control your brand.
https://oyelabs.com/doorda...
#FoodDelivery #OnDemandDelivery #startup #WhiteLabelApp #RestaurantTech
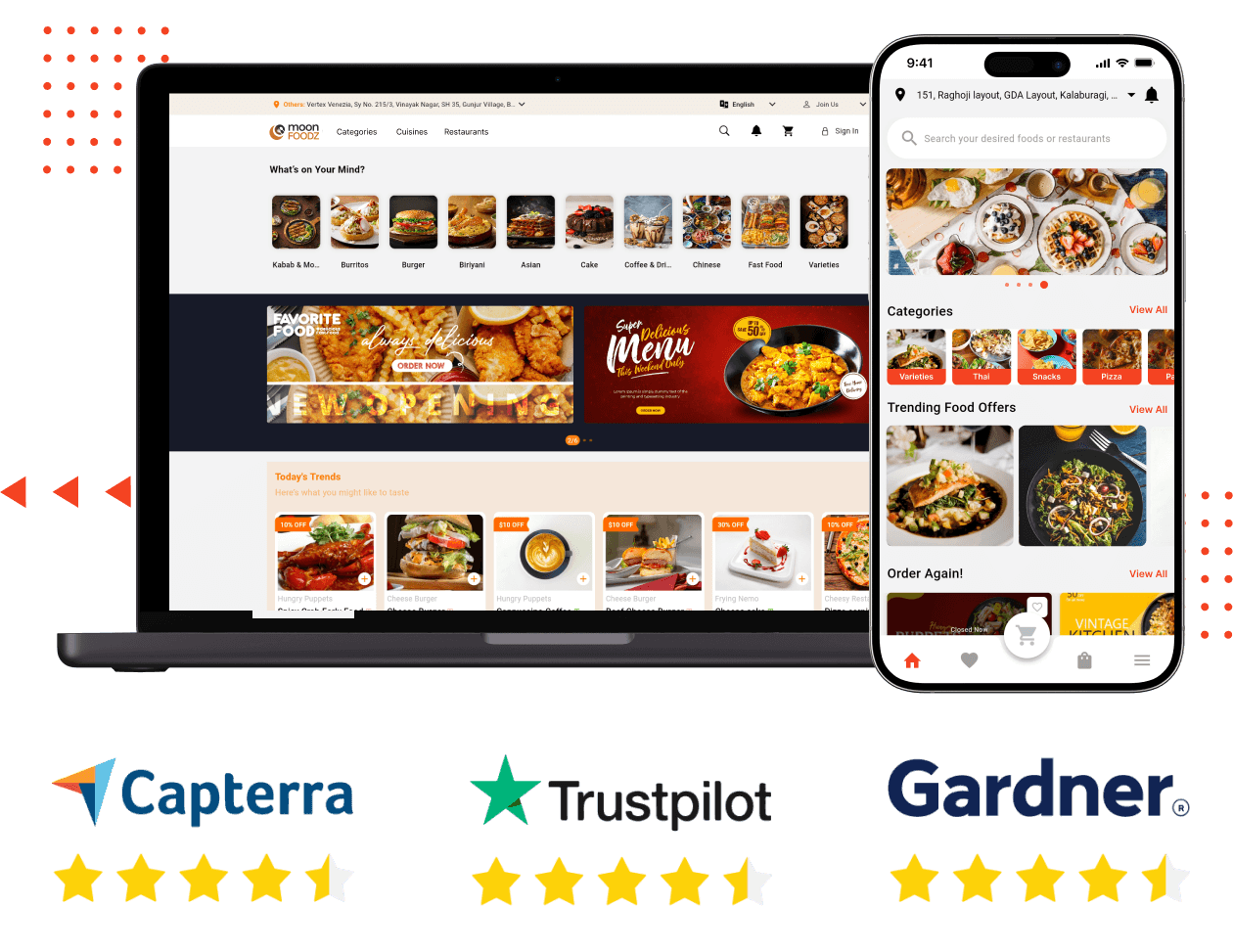
Doordash Clone - Readymade Food Ordering and Delivery App
Doordash clone script is loaded with new-gen features and comes with 100% customizability and free support for 30 days. Launch food delivery business in 3 days.
https://oyelabs.com/doordash-clone/Want to build a real-time, live-commerce app where creators can stream and sell products like on Whatnot? OyeLabs’ Whatnot Clone offers a scalable, white-label solution with full source code ownership. You get Web, iOS & Android support, low-latency streaming, real-time bidding, inventory sync, seller wallets, and admin analytics — with deployment in just 10 days.
https://oyelabs.com/whatno...
#LiveCommerce #ecommerce #startup #WhiteLabelApp #StreamingStore
Koinkart is the trusted choice for launching a beginner-friendly copy trading clone software that helps users follow top traders with confidence. Our platform is designed for smooth trading experiences and easy navigation, making it perfect for new investors and business owners.
Explore the features designed for our clients:
Ultra-fast trading engine
Secure fund management
Multi-payment gateway
Automated trade mirroring
Launch a scalable platform that offers advanced trading speed and unmatched user convenience.
Get Live Demo or Quote Now!
Website: https://www.koinkart.org/c...
WhatsApp: +91 93842 63771
Mail: businesskoinkart.org
Develop an Uber for Handyman app with easy scheduling, verified professionals, and secure payments to streamline home repairs and grow your on demand service brand.
Visit our website:
https://whitelabelfox.com/...
#UberforHandymanServicesApp #UberLikeAppForHandyman #handymanapplikeuber #UberForHandyman #HandymanCloneApp #ondemandhandymanapp #uberforhandymanservices #HandymanAppDevelopment #ondemandhandymanappdevelopment #handymanappdevelopmentservices
Create, share, and monetize your passion with Trioangle’s TikTok clone app 🚀 that supports vivid video effects, trending challenges, and seamless social integration.
To Know More: https://www.trioangle.com/...
WhatsApp - +91 63796 30152
Email ID - salestrioangle.com
Telegram- https://t.me/Trioangle_Tec...
#tiktokclone #TikTokCloneApp #tiktokclonescript #TikTokLikeApp #ShortVideoApp #VideoSharingApp #SocialMediaApp #AppDevelopment #TikTokAlternative #creatorapp #VideoPlatform #MobileAppDevelopment
Launch a handyman app like Uber with scalable features, real-time tracking, and custom branding. Perfect for startups and enterprises entering the on-demand service market. Visit our website for more Info: https://whitelabelfox.com/...
#UberforHandymanServicesApp #UberLikeAppForHandyman #handymanapplikeuber #UberForHandyman #HandymanCloneApp #ondemandhandymanapp #uberforhandymanservices #HandymanAppDevelopment #ondemandhandymanappdevelopment #handymanappdevelopmentservices #handymanhomeservicescloneapp #ondemandhandymanservicesapp
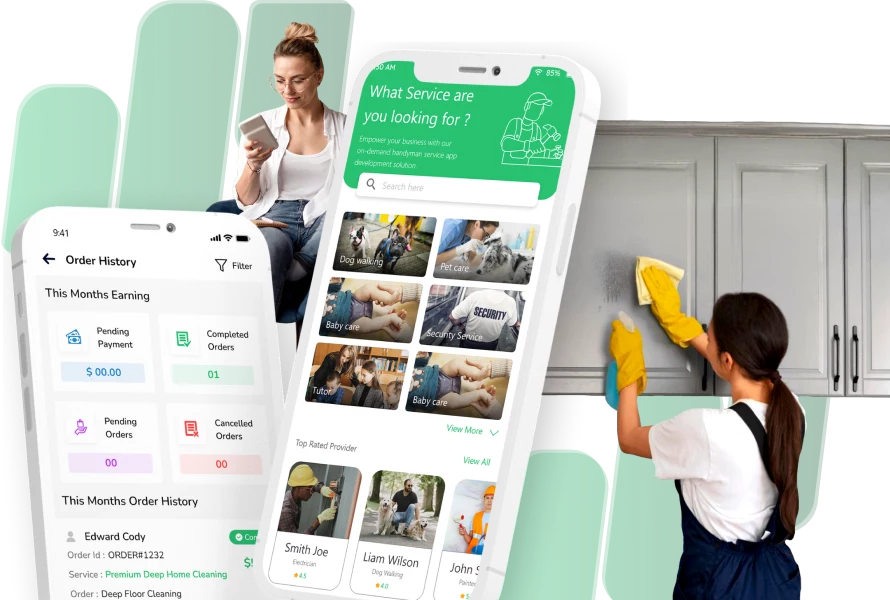
Handyman App Like Uber - Handyman Clone App for You
Looking for a handyman app like Uber? Get our ready-to-launch handyman clone app. All features included! Book a demo today and start your business!
https://whitelabelfox.com/on-demand-handyman-app-like-uber/Visit - https://www.spotnrides.com...
WhatsApp - https://wa.me/919600695595
#Uber for Laundry #LaundryApp #OnDemandLaundry #LaundrySolutions #AppForLaundry #LaundryService #LaundryDelivery #LaundromatManagement #LaundryBusiness #Uber for Laundry App #UberforLaundryServices #LaundryAppClone #OnDemandServices #LaundryAutomation #TechForLaundry #laundromat

Laundry App: Streamline Your Laundromat from Collection to Delivery - SpotnRides - AI Powered Taxi Booking App
A laundry business can witness a remarkable transformation through the integration of technology, particularly with the introduction of laundry apps.
https://www.spotnrides.com/blog/laundry-app-streamline-your-laundromat-from-collection-to-delivery/Build a modern, user-friendly food delivery platform with a customizable DoorDash Clone App designed for fast launch, smooth ordering, and scalable business growth.
https://whitelabelfox.com/...
#doordashclone #DoorDashCloneApp #doordashlikeappdevelopment #doordashclonescript #applikedoordash #doordashcloneappdevelopmentcompany #doordashcloneappdevelopment #fooddeliveryapp

DoorDash Clone App Development | Launch Your Delivery Service
Build a DoorDash-inspired app with our development solutions. Offer a personalized food delivery platform with features to enhance user experience and streamline operations.
https://whitelabelfox.com/doordash-clone-app/